THE ISSUE
On 7 September 2017 Equifax (US) announced that they had had a security breach.
Criminals exploited a web site application vulnerability to gain access to personal information. The breach took place mid-May but was not discovered until 29th July. The incident potentially impacts 143 million US customers
The follow up was that it was later revealed that over 700,000 UK residents (including Yours Truly) had also been hacked as a result of the data breach.
THE COMPANY
Equifax is a US based organisation which is also the second biggest credit-reference agency in the UK, after Experian. Like other similar agencies, it holds information about you which lenders use to assess you when you apply for a mortgage and other credit products.
Equifax holds data on over 44 million people in the UK. This data includes electoral roll, court records, previous credit searches by banks, utilities etc..
The vast majority of people affected by this will never have heard of Equifax, nor had any idea that Equifax had their financial information. The Terms and Conditions for contracts you sign with financial services companies allow this information to be given to Equifax and shared with other companies who check you out for credit products. This may not be a problem in itself, it helps prevent fraud and keeps the cost of credit down for those of us who pay our bills on time and don’t take out credit we can’t afford.
The breach in the US had other, knock on effects:
The theft of Social Security Numbers (SSN) – equivalent to the UK’s National Insurance Numbers – makes it very inconvenient. SSNs track US citizens’ earnings and contributions to the Social Security Program. This is meant to be kept secret. SSNs are very difficult to change, even in extreme cases when they are, so many institutions hold the original number that criminals can still use that information for many years. Whereas a customer can move accounts from a breached organisation – take out another credit card or move to another service provider, you can’t do that with Equifax.
THE GOOD
There are several text-book responses to the Equifax response to the cyber breach, and stood Equifax in good stead when investigations began in earnest.
Called the Police
Equifax reportedly contacted law enforcement agencies immediately.
Called In Independent Security Experts
Equifax contacted a leading independent cybersecurity firm which has been conducting a comprehensive forensic review to determine the scope of the intrusion.
CEO produced YouTube video explaining what happened
The CEO Rick Smith produced a video which explained what had happened and what they were doing about it.
Offered Free Identity Theft protection for 1 year Free of Charge
Equifax offered every customer Free Identity Theft protection for 1 year free of charge via one of their subsidiaries.
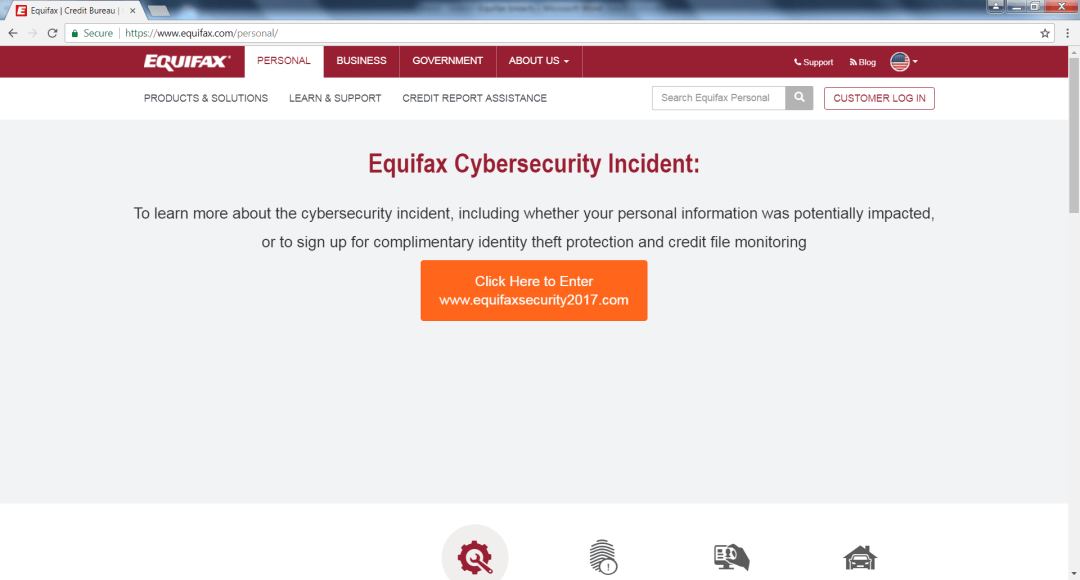
Made it clear on the US web site that there was a breach and what customers could do
The US web site gave an update on what had happened and re-directed customers to another site to check if they had been affected.
The web site was clear and they didn’t try to hide the fact that they’d had an issue.
Explained to different stakeholder groups what had happened and how it affected them
Equifax provided responses tailored to different stakeholder group, not just consumers, by creating 3 separate FAQs (consumers, investors and general questions).
Upgraded customer service response
The contact centre was tripled in size for to 2000 staff to cope with customers questions.
Leveraged Social media
The extensive use of Social media actually answered individual’s questions and updated their crisis web site to address customers’ complaints.
THE BAD
Equifax had the, very rare, luxury of time to prepare its response to this incident. Given that the breach was discovered on 29th July and not reported until 7th September, they had almost 6 weeks to respond to this whereas in many situations an organisation has a matter of hours.
With this in mind it is disappointing that the response had the following shortcomings.Delays in publicising the breach
The original breach was mid-May but not discovered until 29th July had already left their customers vulnerable for approximately 10 weeks. To delay highlighting the issue for another 6 weeks was poor, especially as fraudsters tend to use the information quickly before the breach is discovered.
It is a careful judgement call about when to release information. You need to be sure of the information as much as possible but be prompt enough to limit the damage to customers.
We don’t know when Equifax found out the scale of the breach; it may have been a month ago or just before the 7th September. It may also be the case that they were prevented from announcing earlier by the law enforcement agencies.
Made no change to the Equifax UK web site
Although the web site response to US was effective, the UK site had no reference at all to the incident, not even on the press releases page.
Equifax believed at the time that no UK accounts have been compromised. This turned out later to be false. But in order to appear open and transparent, there should have been sort of notification.
Not appreciating the customer point of view
The link from Equifax to the cyber security incident web site resembled something a hacker would use. Therefore customers were concerned about clicking on this from an organisation which has admitted that it has already been hacked.
Unfortunately, given that the site was newly created and understandably visited by a very large number of concerned consumers, many security sites recognised this activity as being consistent with a phishing site and automatically blocked it.
Furthermore, customers were then asked to put in their last name and last 6 digits of their Social Security Number into this site. This is an unfair response, especially for an organisation that has demonstrated that it can’t be trusted with that information.
If the customer did progress, despite the misgivings stated above, they got a response which said no impact or gave an ambiguous response, thus leading to more questions and concerns.
Unresponsive Contact centre staff
The call centres weren’t up for the task, despite the ramp up of staff. Many customers want to speak to an individual and address their concerns and find out about their particular situation.
Inevitably, in an incident of this kind, contact centres were overloaded and customers were kept waiting or randomly disconnected. Where customers did get through agents were not prepared to give answers to individuals, but redirected customers to the web site. Again, the company had time to step up an emergency response, even at the risk of the information leaking before they preferred.
Didn’t clarify legal position
Part of the terms and a condition of the Equifax offer for 1 year free identity theft protection require them to settle disputes through arbitration, and bans them from participating in class-action lawsuits.
Equifax have since clarified that these terms and conditions will not apply in this case, but still provided confusion and anger in an already sensitive situation.
Monitoring your credit is a typical response to being informed of a breach, but when it’s the credit monitoring agency that has just been breached, customers may be reluctant to continue to trust the organisation.
Didn’t come over as sincere
Video is always a controversial strategy. When done well, it can work. In this case, whilst the CEO Rick Smith got his message over, it looked very stilted as he was obviously reading from a teleprompter and therefore looked wooden and this limits the impact of his apology.
If you are using a video response, you want to connect on an emotionally relatable level to the people watching; using a teleprompter so obviously reduced this immensely.
Limited media & press response
When retailers get hit by a breach like this, it’s a single credit card or login ID and password that might get stolen. When Equifax got breached it could be everything about the affected parties, and presumably linked to other things.
It seems that, other than social media and web site updates, there was little response to media responses for interviews. This may be remedied in the next few days, but in cases like this which have such wide effects and implications; the CEO should have been on every news outlet available for 48 hours.
Insufficient response
CEO said “while we’ve made significant investments in cybersecurity, we have more to do and we will.” This type of response may be appropriate in an event which has less consequence for their customers. The obvious response is “If you realize you have more to do, why didn’t you do it?”
The offer of identity theft protection is virtually useless, due to the high number of breaches there have been (especially in the US), and the fact that the hackers have all they need already – Name, Date of Birth, Social Security Number and Mother’s maiden name – to create a false ID at any time in the past or future.
Senior managers abused their position (allegedly!)
In July, before the incident was made public, three Equifax senior executives sold shares in the company worth almost $1.8m.
Chief financial officer John Gamble sold shares worth $946,374 and president of US information solutions Joseph Loughran exercised options to sell stock worth $584,099.
The president of workforce solutions Rodolfo Ploder also sold stock worth $250,458.
Equifax deny that these senior executives knew anything about the breach and it was just coincidental. Whilst this may be true, but unlikely, the company could have introduced a closed period for senior managers and execs to limit this risk.
Didn’t maximise the impact of Social Media
Whilst Equifax stood up a large social media team to respond to customer concerns they:
- Didn’t link this to the main twitter feeds thus losing much of the impact of their response
- Responded to each tweet with the same approved messaging.
It would have been stronger and less cumbersome had they triaged the inquiries and responded accordingly, in a way that is easily accessible to everyone, rather than individually.
THE LESSONS
This just goes to show that even with:
- The resources of Equifax, a huge financial organisation,
- the time to make rational decisions and
- the advice of security experts and law enforcement…
it is still easy to get incident response badly wrong.